WireGuard is quickly gaining popularity in the VPN marketplace due to its speed, simplicity, and modern cryptography standards. Starting with FreeNAS version 11.3-RC1, it is possible to connect your NAS directly to a WireGuard network with a few easy steps.
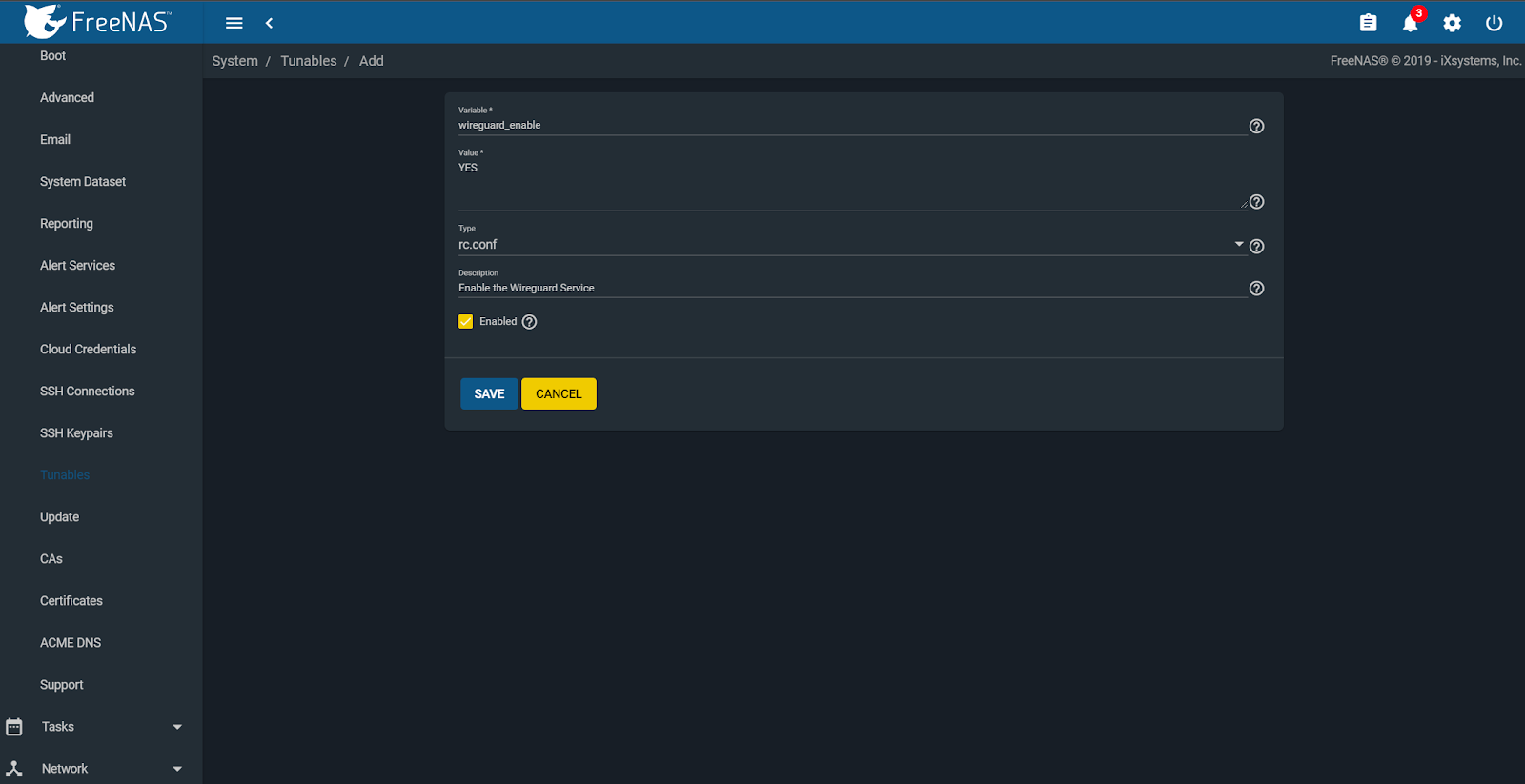
We get started on this by creating some custom tunables to enable the WireGuard service and give it a default interface. To do this you must first navigate to System -> Tunables -> Add.
Enable the WireGuard service by adding “wireguard_enable” -> “YES” in rc.conf.
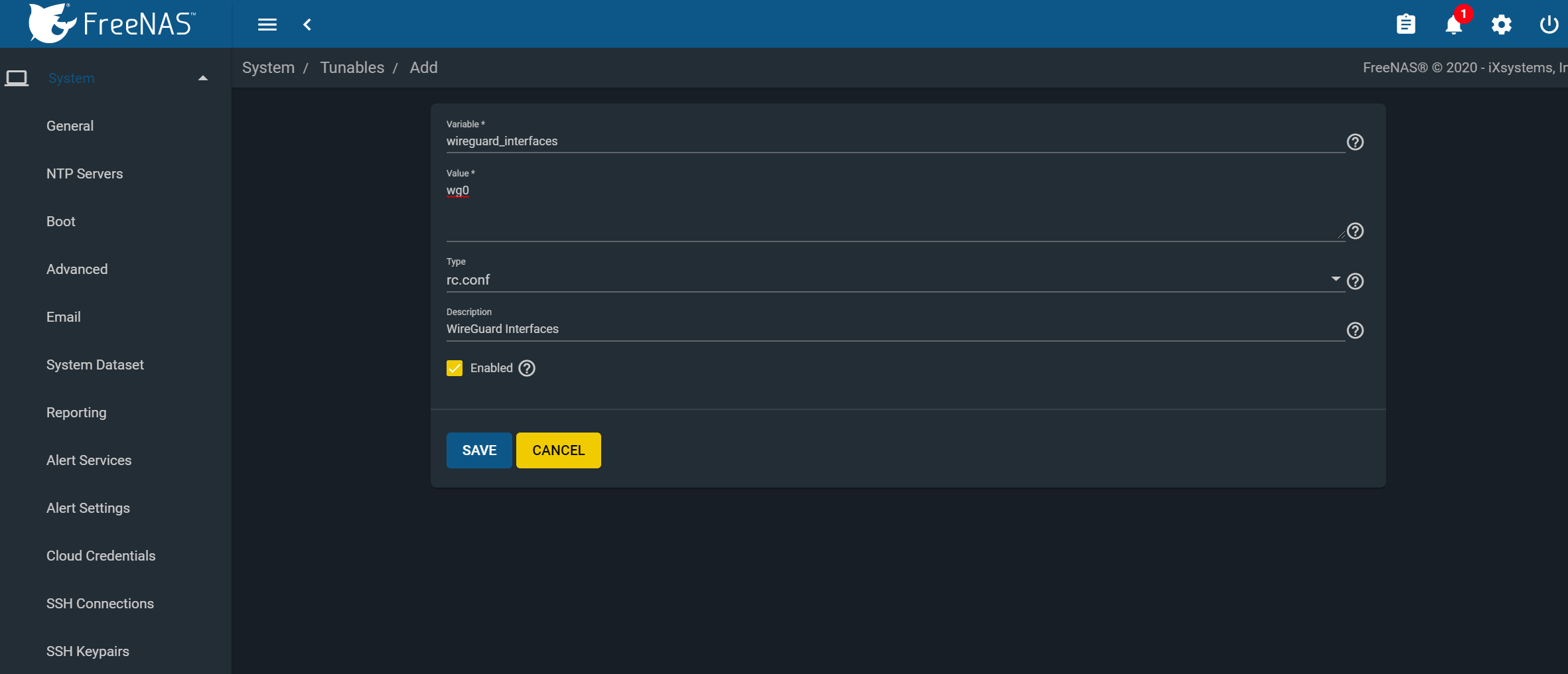
Next, create another tunable and add “wireguard_interfaces” -> “wg0” in rc.conf.
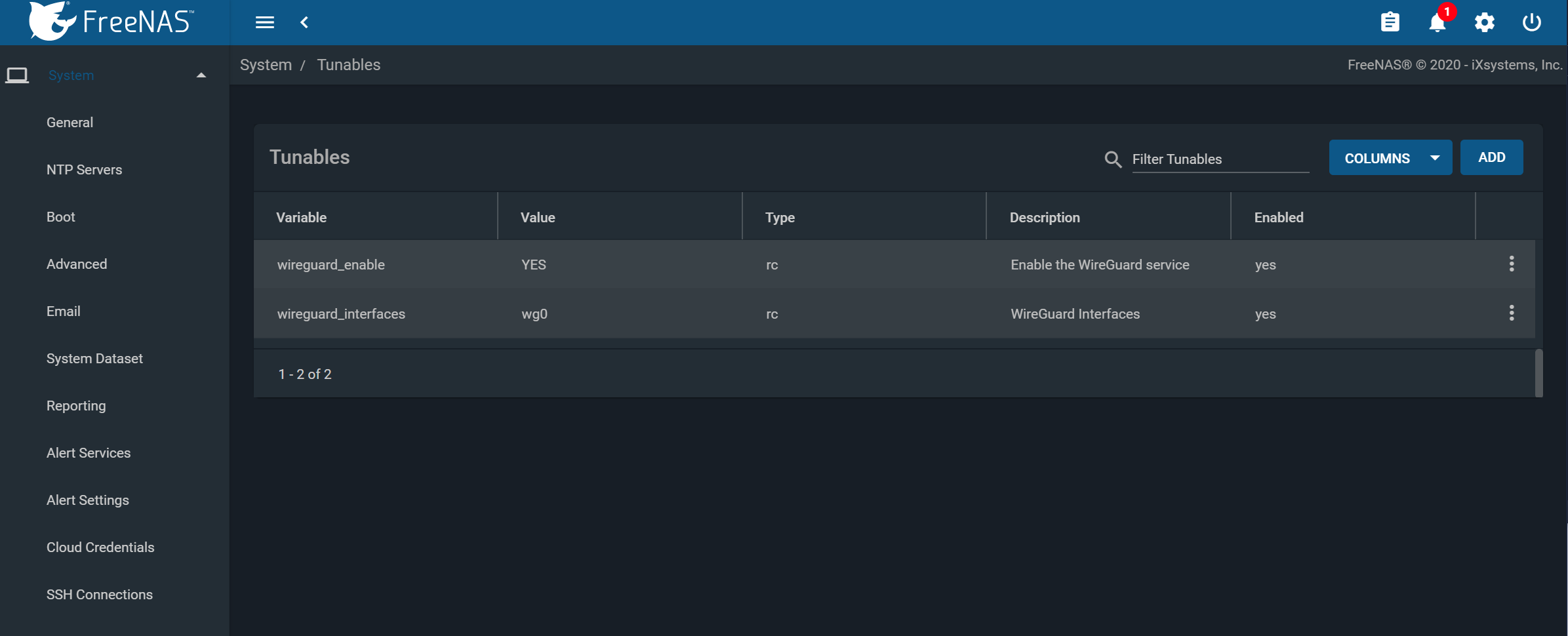
When finished, you should have the following two variables set and enabled.
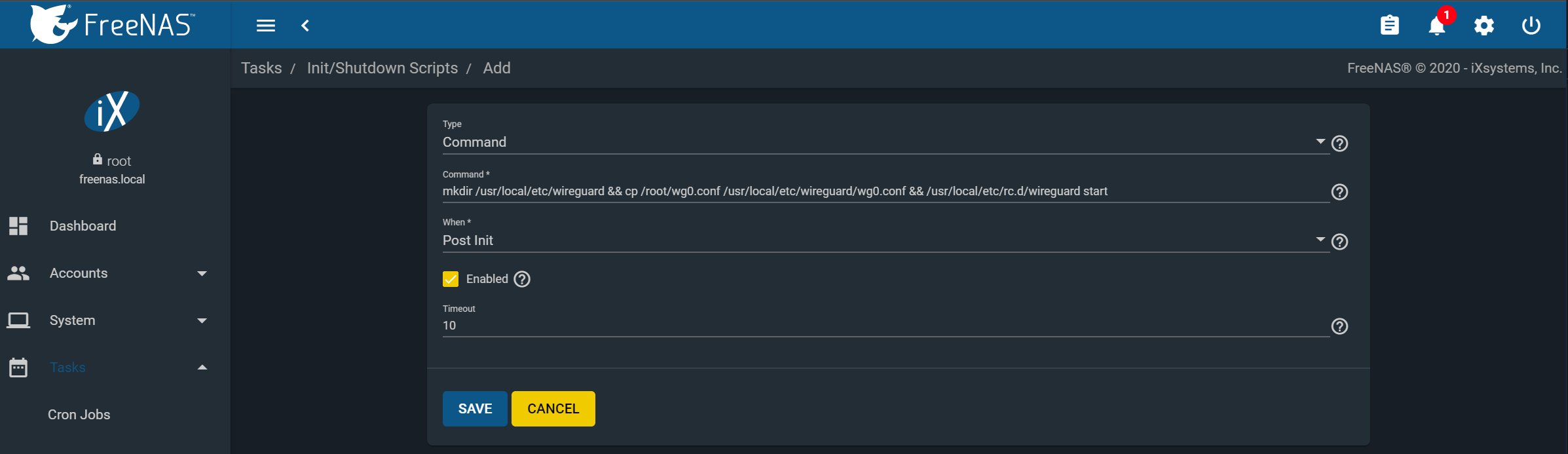
Next, we will need to create a post-init script that will place the WireGuard config into the correct location at startup. Navigate to Tasks -> Init/Shutdown Scripts -> Add.
Create the following command and set it to run at post-init:
“mkdir /usr/local/etc/wireguard && cp /root/wg0.conf /usr/local/etc/wireguard/wg0.conf && /usr/local/etc/rc.d/wireguard start”
You can configure the /root/wg0.conf file and apply a WireGuard configuration to attach to whatever WireGuard network you define. It can be a single point-to-point to anything running WG, or even with full routing. Example use cases are:
- Access data on a NAS from your Remote Laptop
- Linking NAS to NAS for replication
- Attaching a managed NAS to a remote network
- Access to your NAS from your smartphone
We need to create the /root/wg0.conf which will contain the specific WireGuard configuration to apply at boot. This configuration is beyond the scope of this article, but there are quickstart guides and tutorials available online as well as the built-in ‘wg-quick’manpage.
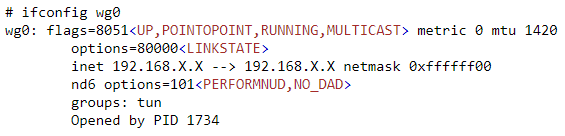
Once you have a valid /root/wg0.conf, rebooting the system should bring up the WireGuard interface, and you’ll see a ‘wg0’ device in the output of ‘ifconfig’.
Congratulations, you have successfully linked your FreeNAS system to a secure WireGuard tunnel!
