NickF
Guru
- Joined
- Jun 12, 2014
- Messages
- 763
Perhaps this is a larger discussion, but I thought I might start in a thread here and reddit, and see where it goes. I may have never even noticed this, except the built in NoVNC is broken in BlueFin RC1.
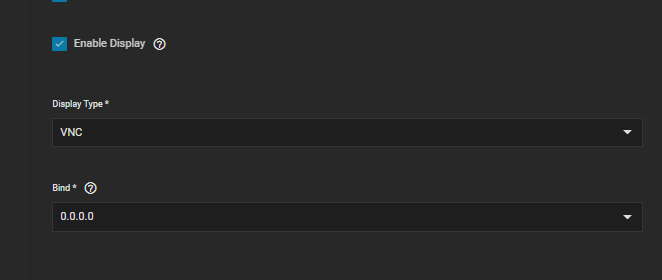
The current implementation for the out-of-the-box deployment of VNC is a little off-putting to me. By default, when you create a VM via the wizard it adds a VNC monitor to your VM so you can manage your box to set it up. This is helpful and I'm glad this feature was implemented, but there is no indication that a password can (and should!) be set for accessing your vms. These passwords are basically useless anyway, but they should at least be an option in the wizard...
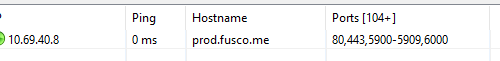
So, in the out-of-the-box deployment of a VM anyone on your network can scan your VM host and gain console level access to all of your VMs without any form of authentication. It seems that TrueNAS puts the VNC ports starting at 5900 (which is common for VNC) and working up. So heres mine as an example:
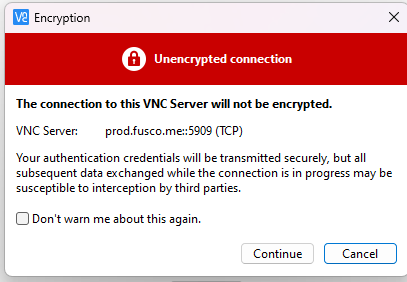
Another thing that is rather disappointing addition to this is that all of the VNC traffic is wholly unencrypted, why is SSL not enabled?
This is very discouraging. If IX is committed to using VNC, rather than reinvent the wheel, I am on board. But you should really only be able to access the VMs from the local host using noVNC...then at least only administrators of the TrueNAS server can access this resource. Maybe a toggle switch can be added to change the firewall rules to allow external VNC connections if people want it. The system should just be secure by default.
The current implementation for the out-of-the-box deployment of VNC is a little off-putting to me. By default, when you create a VM via the wizard it adds a VNC monitor to your VM so you can manage your box to set it up. This is helpful and I'm glad this feature was implemented, but there is no indication that a password can (and should!) be set for accessing your vms. These passwords are basically useless anyway, but they should at least be an option in the wizard...
So, in the out-of-the-box deployment of a VM anyone on your network can scan your VM host and gain console level access to all of your VMs without any form of authentication. It seems that TrueNAS puts the VNC ports starting at 5900 (which is common for VNC) and working up. So heres mine as an example:
Another thing that is rather disappointing addition to this is that all of the VNC traffic is wholly unencrypted, why is SSL not enabled?
This is very discouraging. If IX is committed to using VNC, rather than reinvent the wheel, I am on board. But you should really only be able to access the VMs from the local host using noVNC...then at least only administrators of the TrueNAS server can access this resource. Maybe a toggle switch can be added to change the firewall rules to allow external VNC connections if people want it. The system should just be secure by default.
