I think we may be hitting an impasse soon.. but I'll bite.
Certainly on ESXi, a proper hypervisor, but TrueNAS is a NAS OS at heart, with layers on top, those layers add extra layers and complexity and exploitability and layers many of us may not see or understand.
I do hear your point here...But I think you are making some improper assumptions.
- KVM, the hypervisor in SCALE, is a highly mature offering using in the Enterprise and the Cloud...soooo I don't understand?
- I think that you'll find that is the opposite of the direction TrueNAS SCALE is going. The developers have shown that they are very much taking security seriously...as evidenced by loads of new official documentation in that regard.
- I think you will also find that the developers have shifted focus to removing packages to decrease the security footprint, while maintaining features through apps in k3s. This is especially apparent in the recent Cobia beta.
If you think of SCALE more like Proxmox with a storage-focused UI (and better a much better one in general imo), rather than as some nebulus blob you don't undersyand....I think you might change your tune. This isn't a far-fetched correlation. They are both based on Debian, they both use KVM, the both have the ability to host containers (LXC vs k3, but containers), they both have ZFS support and they are both offered in "Production Environments" and "Homelabs" The big difference here is Proxmox can do more stuff, but it's also alot more fiddly. Whereas, as you rightly pointed out, TrueNAS is designed as an appliance so all those crazy bells and whistles are not available.
FWIW you can run "Entperise" level firewall/networking products on KVM. If they didn't think it was secure enough to offer that in their supportability matrix, they certainly would not. And those folks driving those decisions are much smarter than you or I. Example: https://docs.paloaltonetworks.com/v...ployment/set-up-the-vm-series-firewall-on-kvm
When it comes to exploits or getting hacked, it is not a matter of if, but when. I know most people figure they don't have anything important in their home networks or think "but why would someone hack me" not realizing it is a bot army out there scanning 24/7 the world looking for an exploitable system to show up on the internet and not until they do get hit, then have the light bulb moment of "Oh crap....I didnt have that backed up anywhere else"
I do not and have not disputed this claim? If anything, my rather lengthy posts should illustrate that I know and understand this. In each of those examples I am demonstrating the use of firewalls inside of firewalls. I am a huge advocate for generally taking network segmentation to a level far beyond just VLANs or other basic things. Security in layers, and all. If you'd like, we can sidebar on the benefits of PacketFence...the other pf...(Open source Cisco ISE)

I block in and out on my PfSense purely for numbers to se (need to get my SIEM back up one day to get real details) but this is over just 10 days in/out
Sure. We are in agreement. Although, I think far more is to be said about Suricata than pfBlocker...(or better still, even ZenArmor if you want to get crazy). But for the record...you can run pfBlocker on a pfSense firewall...regardless of whether it's on bare-metal or in a VM. Your appeal to your general sense of the importance of security is good, but it does not have anything to do with the question at hand.
Also, FWIW on the "TYPE 1" VS "TYPE 2" bit. KVM is literally listed as a "Type 1" hypervisor.
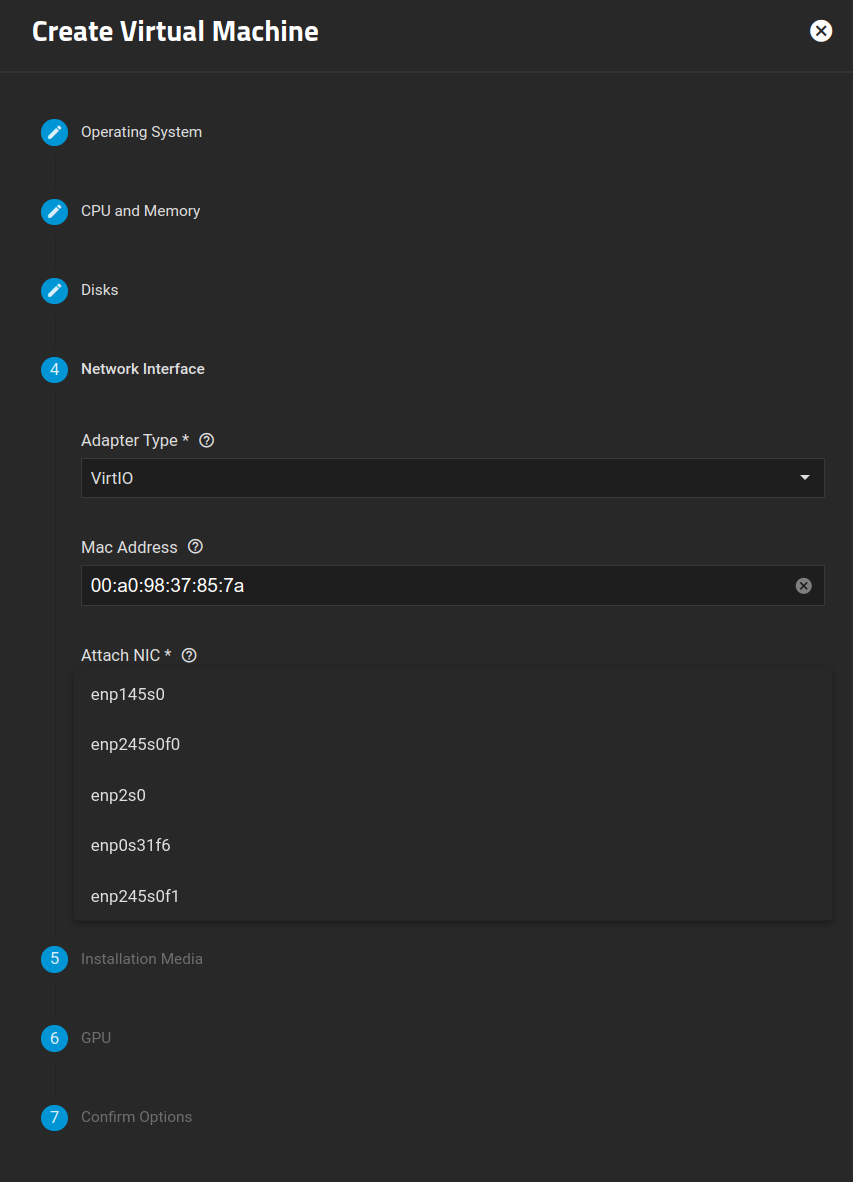
I'm sure we can have some semantical arguments on whether or not KVM running on a host OS like TrueNAS or even Hyper-V running on a phat install of Windows Server can even truely be considered "Type-1" hypervisors. We can also make semantical arguments that the source I cited there is invalid. In either case, lets consider some potential arguments there. We can even make the argument that the above screenshot shows that KVM is also a Type-2 hypervisor.
If you are willing to make the above argument, wouldn't you also have to conclude that anything that calls itself "hyperconverged" should not be definitionally considered TYPE-1 hypervisors either? And I don't think anyone is claiming that point. Seeing as how VMWare VSAN exists and everything.
Given the inconsistencies... We can infer a bunch. Rather than try to re-define KVM as a "True" Type-1 hypervisor...(the very fact that I have to put that in air-quotes there to convey this argument sorta proves my point)...let's focus on what matters. We should not be defining and basing our assumptions of the quality of a hypervisor based exclusively on the "Type" of the hypervisor. It's not really relevant any longer. If it were, "hyperconverged" would not exist...it kinda needs a base OS :)
In any case, imma keep doing me. Feel free to keep doing you. Here's my SCALE box. Dooing pretty well as a hypervisor for my deployment. If you consider not seeing any storage processes really eeking out too much CPU. Consider also, nearly all of my processes consuming CPU cycles are from KVM. This does not look like an example of a bad hypervisor to my eye.
@visamp We've obviously gotten into the weeds here a bit. But this is definitely absolutely all relevant to the spirit of the questions you are asking...even if not direct answers.