Certificates Authorities Screens
8 minute read.
The Certificate Authorities widget on the Credentials > Certificates screen displays certificate authorities(CAs) added to TrueNAS and allows you to add new CAs, or download, delete, or edit the name of an existing CA.
The download icon downloads the CA to your server.
deletes the CA from your server.
Each CA listed on the widget is a link that opens the Edit CA screen.
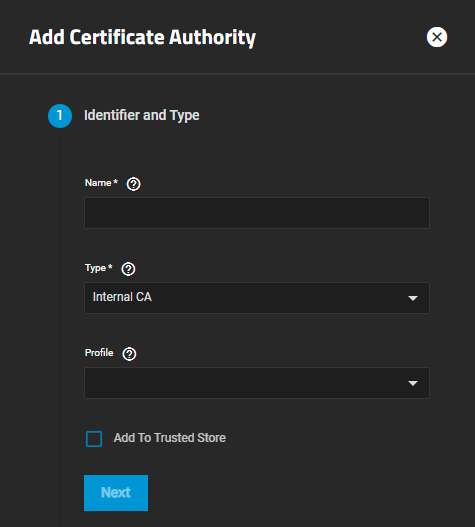
Add opens the Add CA wizard that steps you through setting up a certificate authority (CA) that certifies the ownership of a public key by the named subject of the certificate.
The Add CA wizard screens step users through configuring a new certificate authority on TrueNAS. The wizard has five different configuration screens, one for each step in the CA configuration process:
The Identifier and Type options specify the CA name and choose whether to create a new CA or import an existing CA.
Users can also select a predefined certificate extension from the Profiles dropdown list.
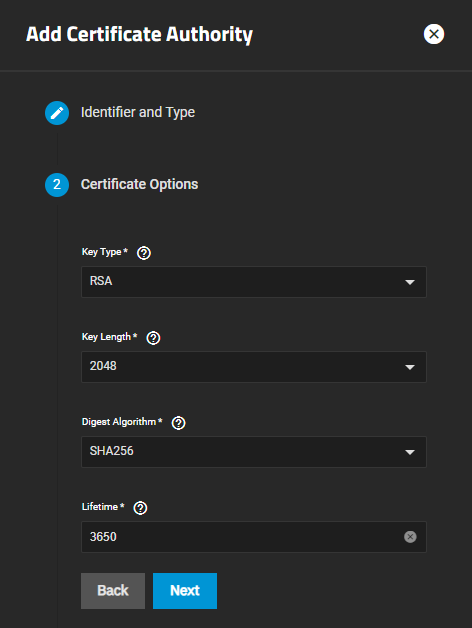
The Certificate Options settings specify the type of private key to use (as well as the number of bits in the key used by the cryptographic algorithm), the cryptographic algorithm the CA uses, and how many days the CA lasts.
The Certificate Options settings do not display if Type on the Identifier and Type screen is set to Import CA.
The Key Type selection changes fields displayed. RSA is the default setting in Key Type.
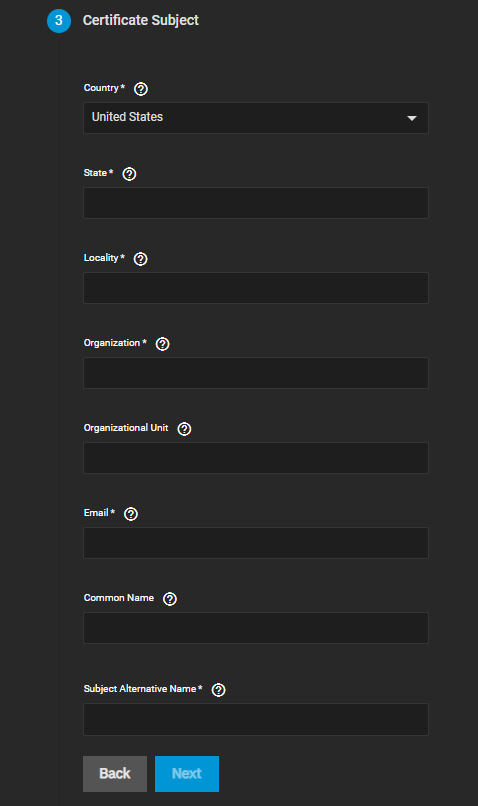
The Certificate Subject settings define the location, name, and email of the organization using the certificate.
Users can also enter the system fully-qualified hostname (FQDN) and any additional domains for multi-domain support.
The Certificate Subject settings do not display if Type on the Identifier and Type screen is set to Import CA.
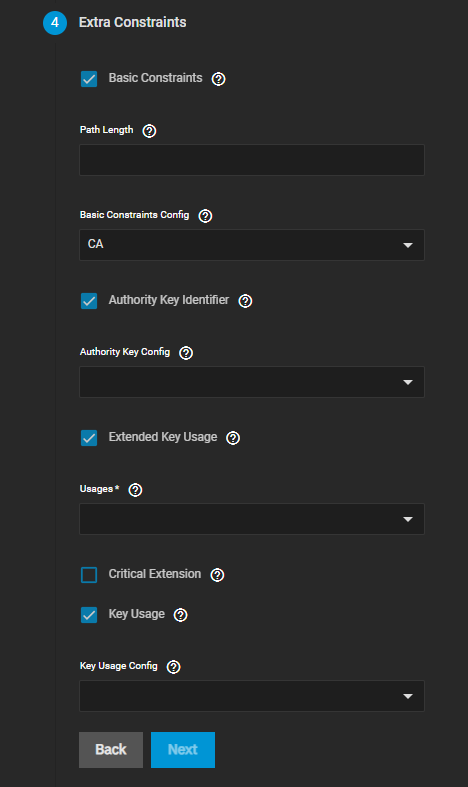
The Extra Constraints options contain certificate extension options.
- Basic Constraints limits the path length for a certificate chain.
- Authority Key Identifier provides a means of identifying the public key corresponding to the private key used to sign a certificate.
- Key Usage defines the purpose of the public key contained in a certificate.
- Extended Key Usage further refines key usage extensions.
The Extra Constraints settings change based on the selection in Type on the Identifier and Type screen.
After selecting Basic Constraints, Authority Key Identifier, Extended Key Usage, or Key Usage, each displays more settings that the option needs.
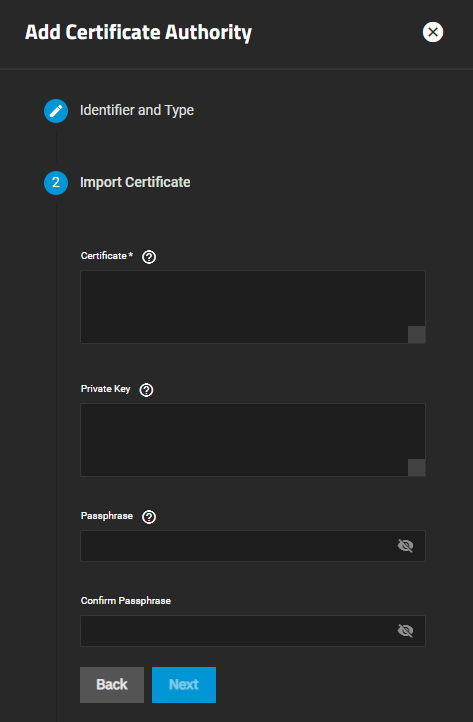
When Type on Identifier and Type is set to Import CA the Import Certificate screen displays.
The final step screen is the Confirm Options that displays the CA Type, Key Type, Key Length, Digest Algorithm, Lifetime, Country, and any configured Usages. For Import CA type, the screen displays Type and Certificate.
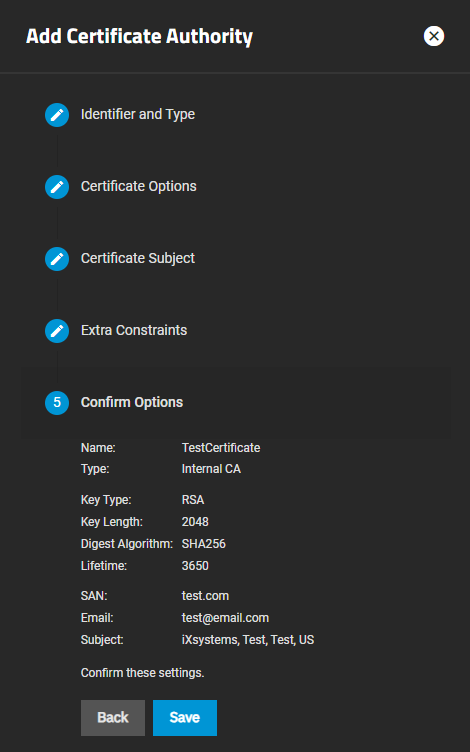
Save adds the certificate to TrueNAS. Back returns to previous screens to make changes before you save. Next advances to the next screen in the sequence to return to Confirm Options.