TrueNAS Early Release Documentation
This content follows TrueNAS 26 releases.
Use the Product and Version selectors above to view content specific to a stable software release.
Directory Services Screens
22 minute read.
The Directory Services screen and widgets provide access to TrueNAS settings to set up access to directory services and advanced authentication systems deployed in user environments.
TrueNAS does not configure Active Directory domain controllers or LDAP directory servers, nor does it configure Kerberos authentication servers or ID mapping systems.
Refer to documentation for these services and systems for information on how to configure each to suit your use case.
The Directory Services screen configuration options set up access to directory servers through domain and account settings, and can set up ID mapping or Kerberos authentication and authorization services.
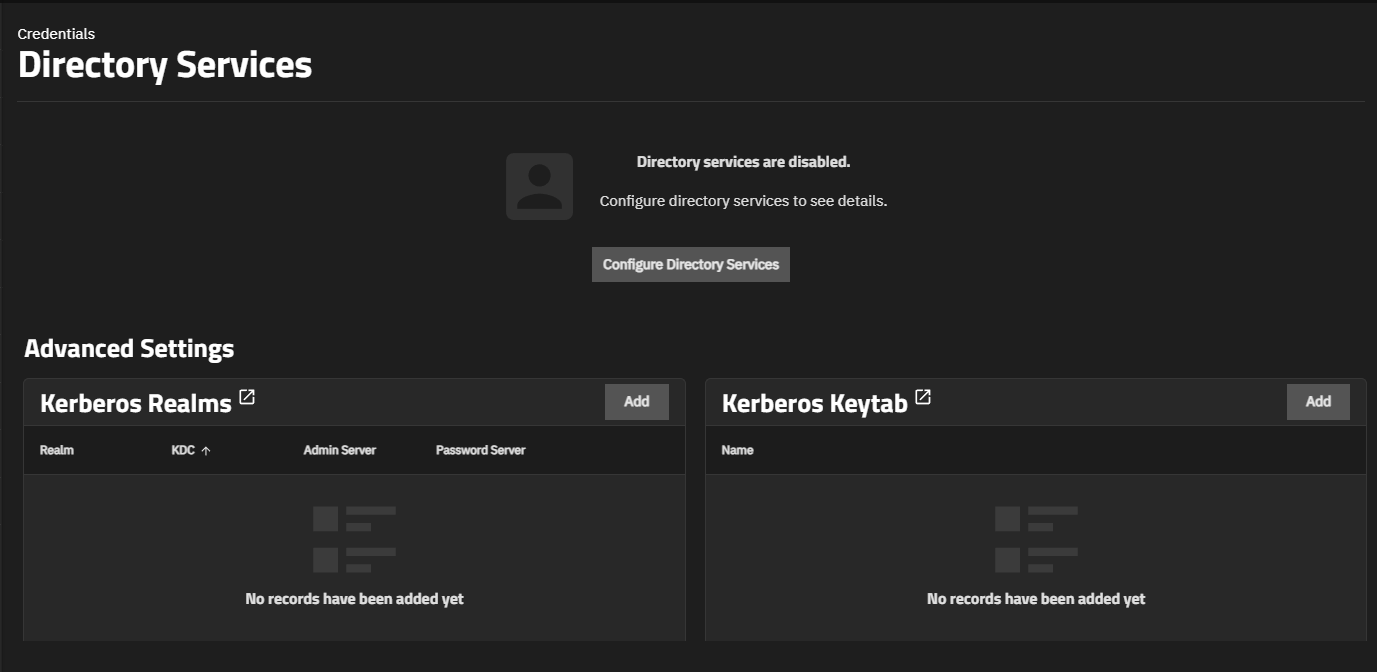
The screen shows the status of directory services when a service is not configured or when it is configured but disabled.
The main option displays:
- Configure Directory Services opens the Directory Services Configuration form where you can set up Active Directory, IPA, or LDAP connections.
- Advanced Settings
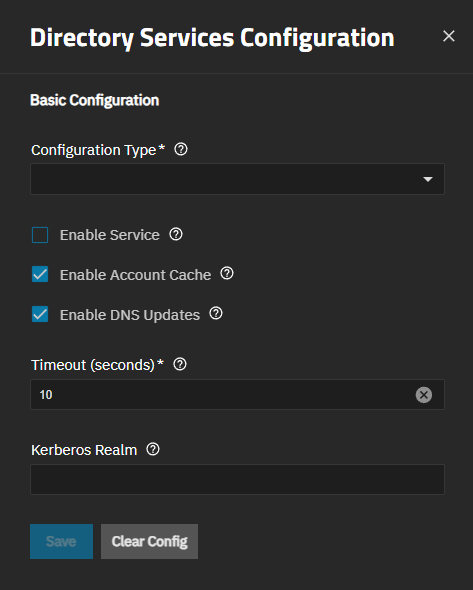
The Directory Services Configuration screen shows common and directory service-specific settings based on the type of directory service selected in Configuration Type.
Common settings:
Directory Service-specific settings:
The Basic Configuration settings show settings common to the three directory services available in TrueNAS: Active Directory, LDAP, and IPA (formerly FreeIPA).
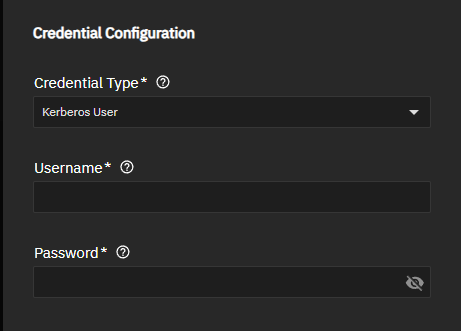
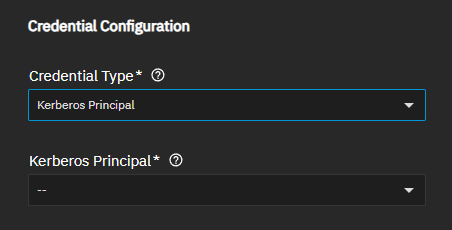
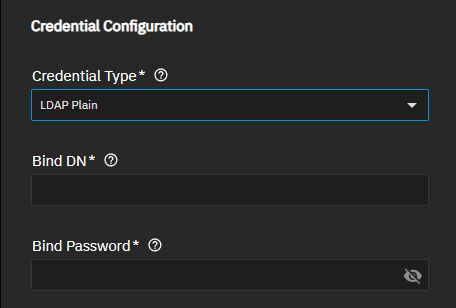
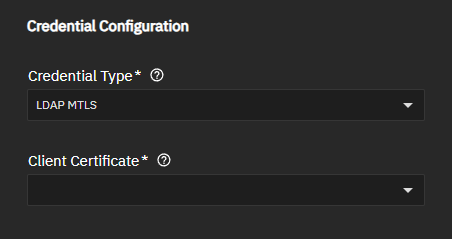
The Credential Type setting changes the authentication settings shown for the directory service no matter which type is selected in Configuration Type. Active Directory, IPA and LDAP all show Kerberos authentication options, but LDAP shows additional settings based on LDAP options.
Credential Type sets the credential used to bind to the specified directory service. Kerberos credentials are required for Active Directory or IPA domains. Generic LDAP environments support various authentication methods. Available methods depend on the remote LDAP server configuration. If Kerberos credentials are selected for LDAP, GSSAPI binds replace plain LDAP binds. Use Kerberos or mutual TLS authentication when possible for better security.
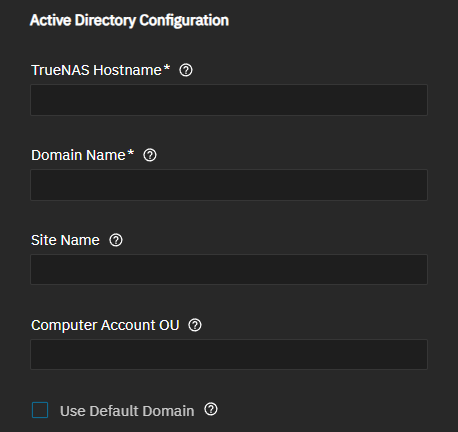
The Active Directory Configuration section settings define the connection parameters and domain-specific options.
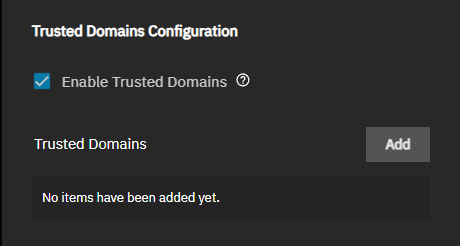
Beginning in TrueNAS 25.10, trusted domains are configured as part of the Active Directory configuration rather than as separate IDmap entries.
The Trusted Domains Configuration section controls access for trusted domains.
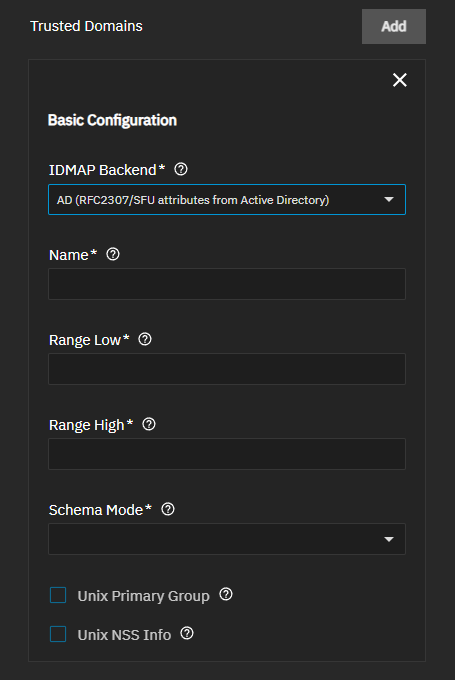
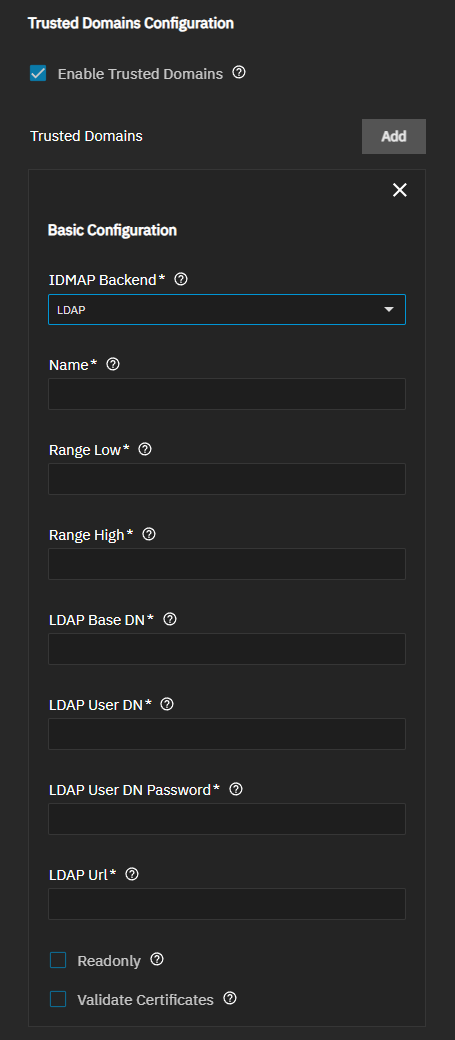
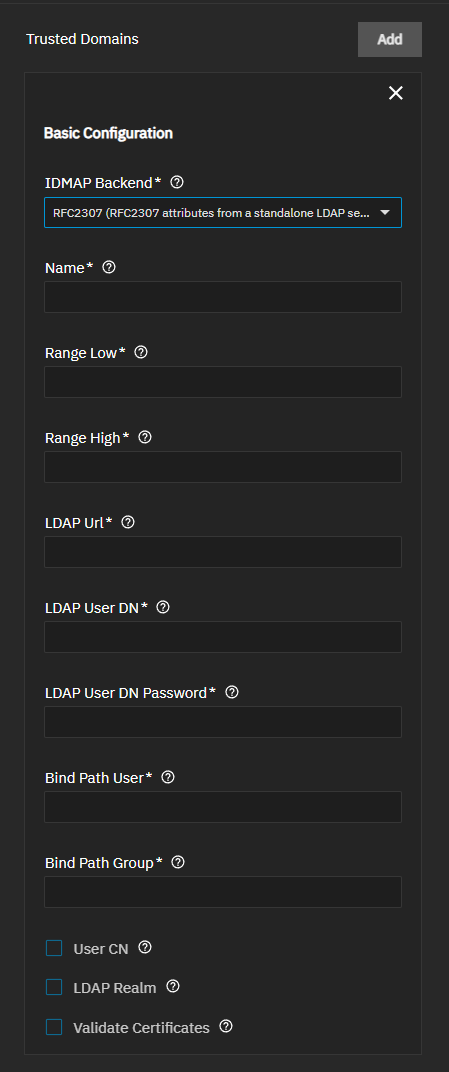
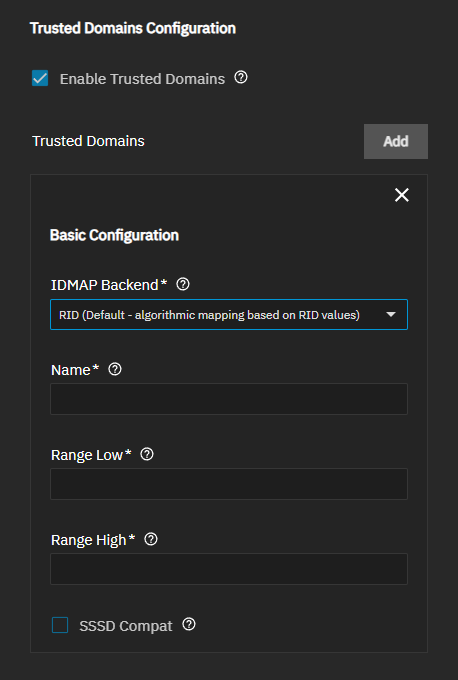
Enable Trusted Domains shows the Trusted Domains options that allow clients to access TrueNAS if they are members of domains with a trust relationship. When enabled, the Trusted Domain section and Add button show. Add shows the Basic Configuration section with the IDMAP Backend options.
The IDMAP Backend configuration defines how domain accounts joined to TrueNAS are mapped to Unix UIDs and GIDs on the TrueNAS server. Most TrueNAS deployments use the RID backend, which algorithmically assigns UIDs and GIDs based on the Active Directory account SID. Another common option is the AD backend, which reads predefined Active Directory LDAP schema attributes that assign explicit UID and GID numbers to accounts.
The IDMAP Backend dropdown list shows four options:
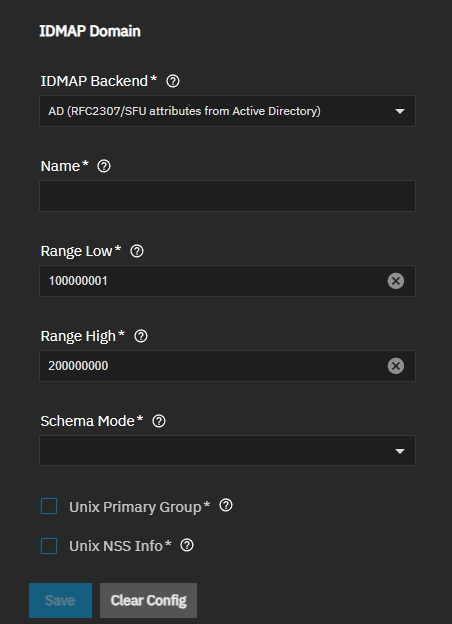
- AD (RFC2307/SFU attributes from Active Directory)
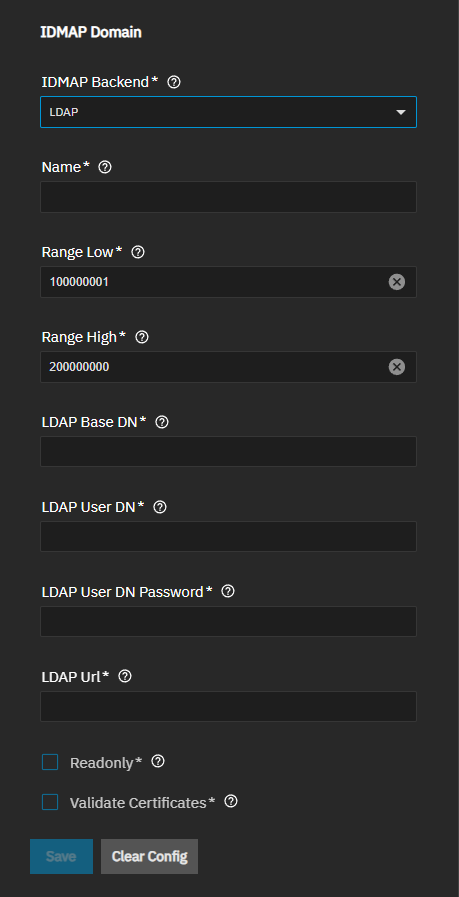
- LDAP
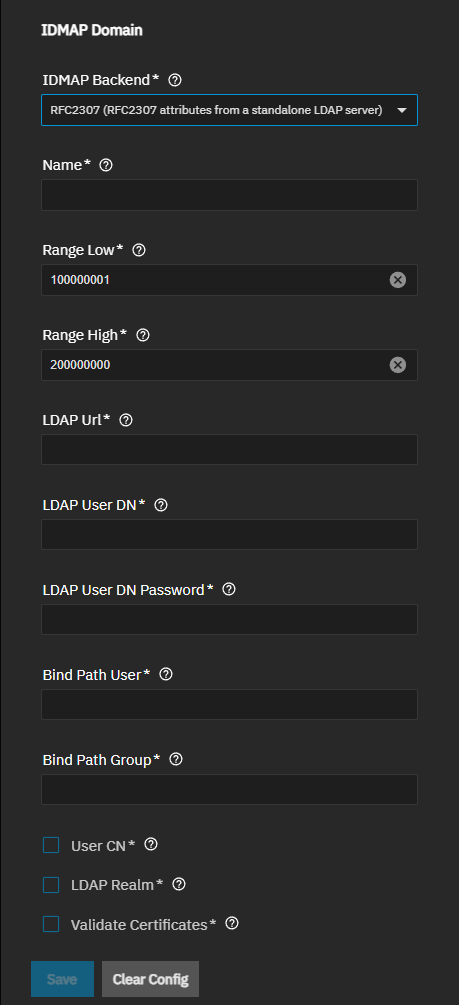
- RFC2307 (RFC2307 attributes from a standalone LDAP server)
- RID (Default - algorithmic mapping based on RID values)
Each option shows different settings.
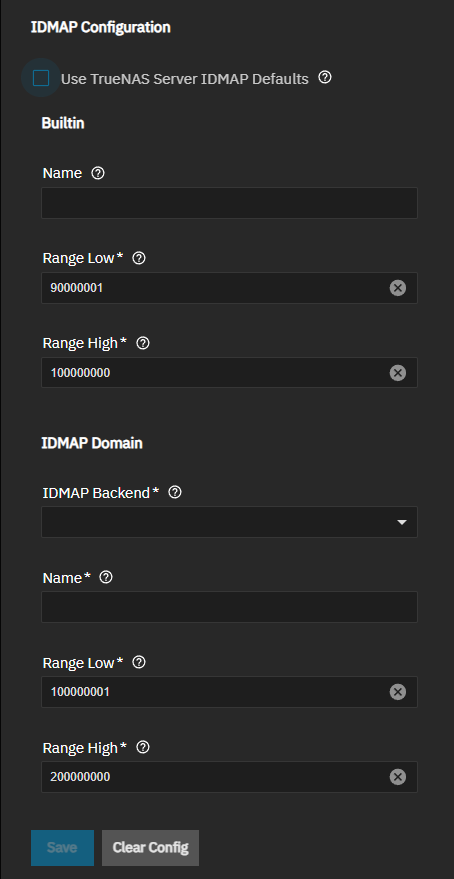
Use Trusted Server IDMAP Defaults is enabled by default. Use the TrueNAS default IDMAP configuration unless you want to customize ID mapping. Defaults are suitable for new deployments without existing support for Unix-like operating systems. The default configuration uses the RID backend with predefined UID/GID ranges (builtin: 90000001-100000000, domain: 100000001-200000000).
When disabled, it shows IDMAP configuration settings to customize ID mapping.
Only administrators experienced with configuring ID mapping should customize IDMAP settings.
The Builtin settings map Windows built-in local groups to Unix GIDs, defining the UID/GID range allocated to Windows built-in local groups, such as Administrators, Users, and Guests. TrueNAS creates this entry automatically when joining a domain. Adjust the range only if it conflicts with existing local UID/GID assignments.
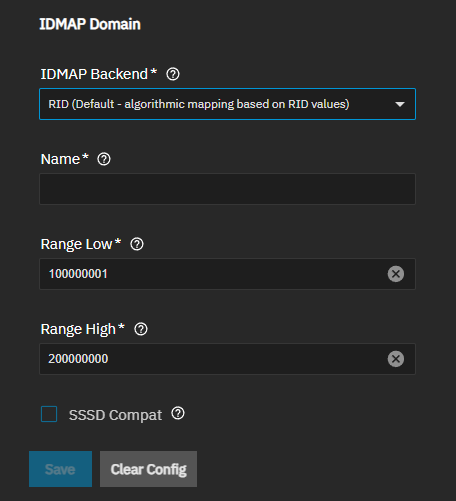
IDMAP Domain settings configure how TrueNAS maps Windows domain users and groups from the joined domain to Unix UIDs and GIDs. The selected backend determines whether mappings are generated algorithmically or read from directory attributes. The UID/GID range defined here must not overlap with local accounts or trusted domain ranges.
The IDMAP Backend configuration defines how domain accounts the domain TrueNAS is joined to are mapped to Unix UIDs and GIDs on the TrueNAS server. Most TrueNAS deployments use the RID backend, which algorithmically assigns UIDs and GIDs based on the Active Directory account SID. Another common option is the AD backend, which reads predefined Active Directory LDAP schema attributes that assign explicit UID and GID numbers to accounts.
The IDMAP Backend dropdown list shows four options:
- AD (RFC2307/SFU attributes from Active Directory)
- LDAP
- RFC2307 (RFC2307 attributes from a standalone LDAP server)
- RID (Default - algorithmic mapping based on RID values)
Each option shows different settings.
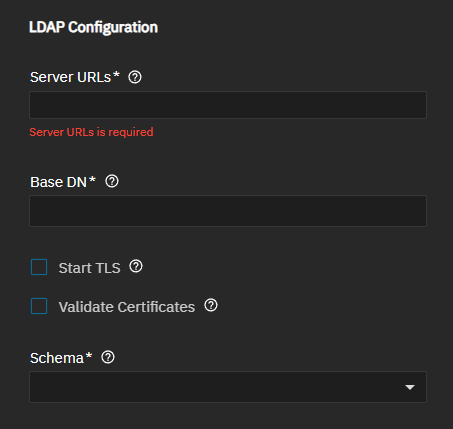
The LDAP Configuration section settings define the connection parameters and validation options.
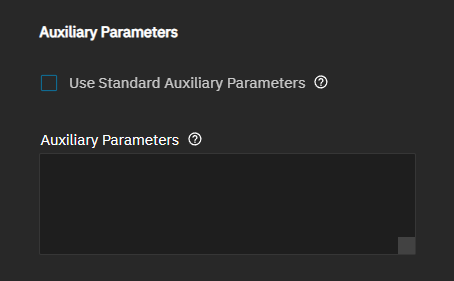
The Auxiliary Parameters subsection allows customization of auxiliary parameters.
Use Standard Auxiliary Parameters is enabled by default. Disable to enter custom options for nslcd.conf.
Auxiliary parameters are an unsupported configuration. Parameters entered here are not validated and can cause undefined system behavior, including data corruption or data loss.
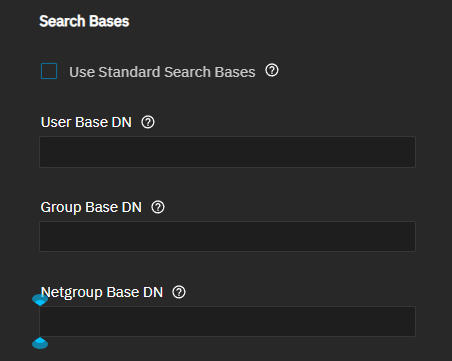
The Search Bases uses standard search bases when enabled. Disable to allows customization of search base DNs. Use the base DN for user, group, and netgroup searches. Disable to specify alternative LDAP search base settings to define where to find user, group, and netgroup entries. Use custom search bases only if the LDAP server uses a non-standard LDAP schema or if you want to limit the accounts available on TrueNAS.
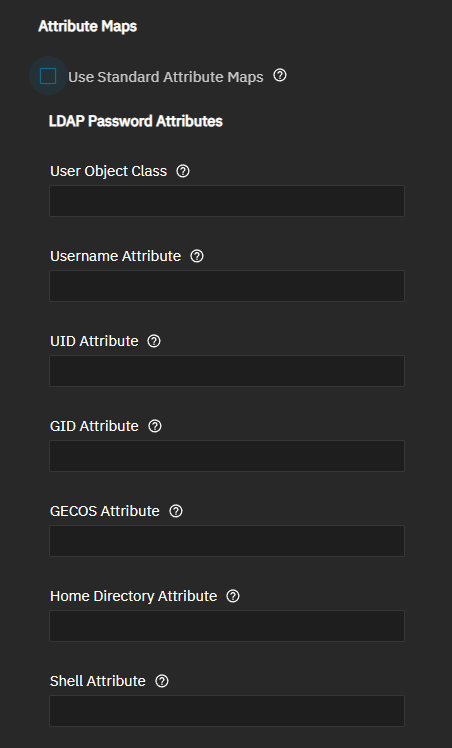
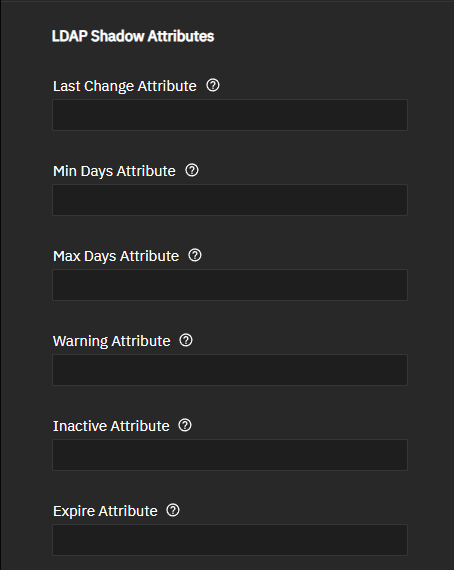
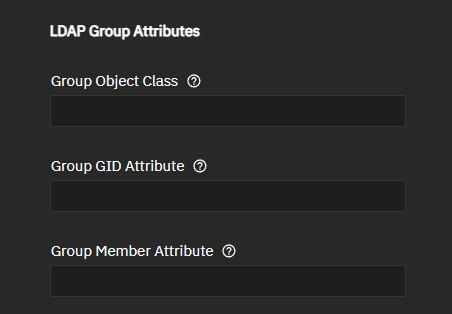
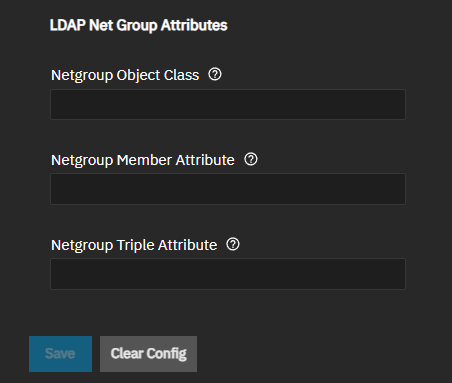
The Attribute Maps settings allow customization of attribute mappings by defining custom LDAP attribute names for user and group account fields. An attribute left blank uses the default attribute name for that field. Only use custom attribute maps if the LDAP server is non-standard, if your LDAP schema uses non-standard attribute names.
Use Standard Attribute Maps is enabled by default, and uses standard RFC2307 or RFC2307BIS attribute mappings. When disabled, the standard LDAP attribute mapping for LDAP servers that do not follow RFC2307 or RFC2307BIS shows to allow for customization.
The screen groups settings into LDAP password attributes, shadow attributes, and group attributes: LDAP Password Attributes, LDAP Shadow Attributes, LDAP Group Attributes, and LDAP Net Group Attributes.
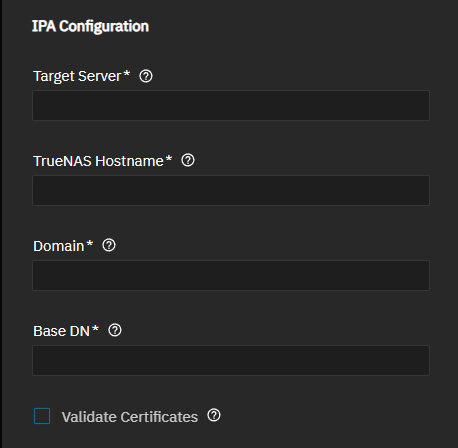
The IPA Configuration settings define the connection parameters and validation options.
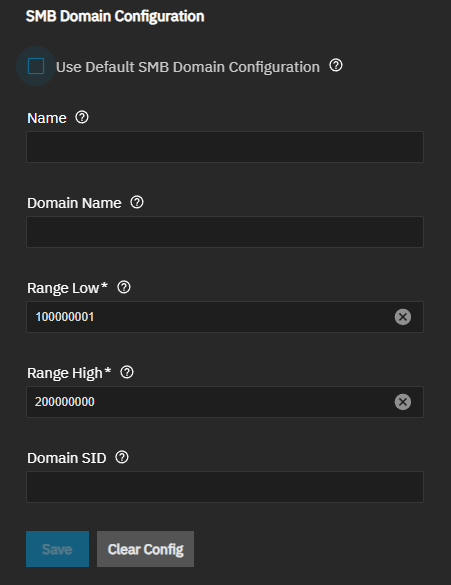
The SMB Domain Configuration settings control SMB integration.
Use Default SMB Domain Configuration is enabled by default, and uses the default SMB domain settings detected during the IPA join. Settings for the IPA SMB domain are automatically detected by TrueNAS during the domain join process. Some IPA domains might not include SMB schema configuration. IPA includes integrated Samba support and can provide user and group information for SMB authentication. Disable to enter custom settings.
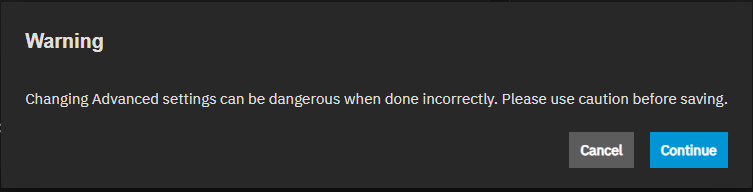
The Show button to the right of Advanced Settings opens a warning dialog stating that incorrectly configuring advanced settings is dangerous. Continue closes the warning dialog.
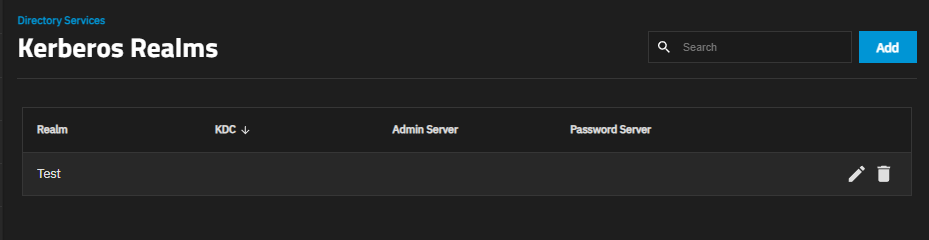
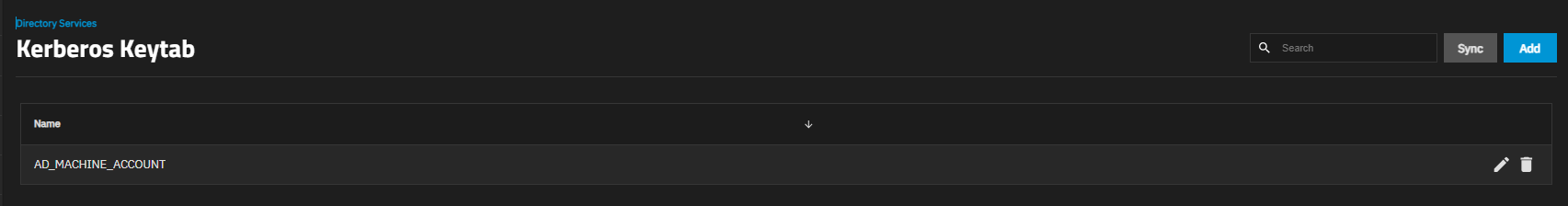
After closing the warning dialog, the Directory Services screen shows the Kerberos Realm and Kerberos Keytab cards.
Each Kerberos card shows the realms or keytabs configured in TrueNAS.
Add on the Kerberos cards opens configuration screens for each Kerberos function:
The Add Kerberos Realm screen allows adding a Kerberos realm to the TrueNAS system.
| Setting | Description |
|---|---|
| Name | Specifies a short name for the Kerberos realm. The Kerberos standard allows upper case characters, DNS rules apply, and does not exceed 253 characters (letters, digits, and/or hyphens). TrueNAS does not enforce naming conventions, but requires entering a name. |
| Primary KDC | Specifies the master Kerberos domain controller for this realm. TrueNAS uses this as a fallback if it cannot get credentials because of an invalid password. This can help in environments where the domain uses a hub-and-spoke topology. Use this setting to reduce credential errors after TrueNAS automatically changes its machine password. |
| KDC | Specifies the name of the Key Distribution Center. Pressing Enter separates multiple values. |
| Admin Server | Defines the server where all changes to the database are performed. Pressing Enter separates multiple values. |
| Password Server | Defines the server where all password changes are performed. Pressing Enter separates multiple values. |
The Add Kerberos Keytabs allows adding a keytab file using the file browser option and assigning the keytab a name.
Name specifies a short name for the keytab on the TrueNAS system. Kerberos does not have a name convention for keytab files.
Choose File opens the file browser to locate and upload a keytab file. Kerberos keytab files are binary files in a specific format (MIT Kerberos keytab format). Keytab files can have either the .keytab or .kt extension.